Zero Trust Security has evolved from a buzzword to a foundational principle for modern IT systems. As cyber threats grow more sophisticated and digital environments become increasingly complex, organizations are recognizing that traditional perimeter-based security models are no longer sufficient. In 2026, Zero Trust is not just a best practice—it’s a necessity for safeguarding sensitive data, ensuring compliance, and maintaining business continuity.
Understanding Zero Trust Security
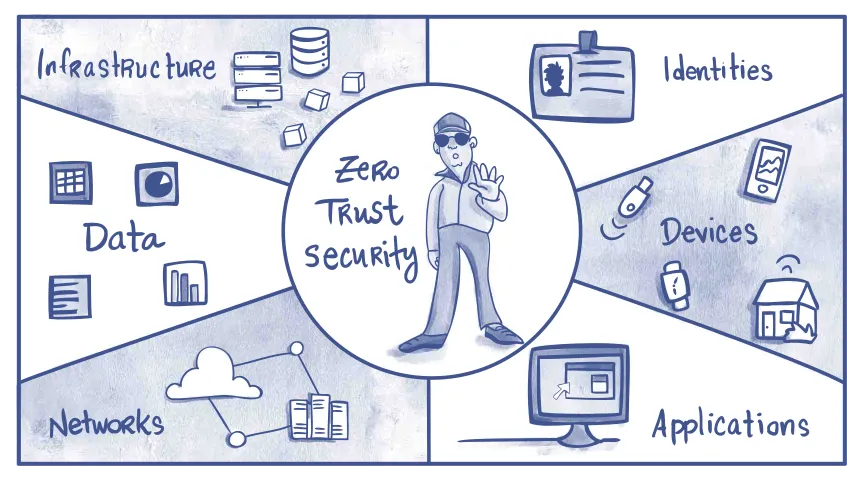
Zero Trust Security is built on the principle of “never trust, always verify.” Unlike legacy models that assume everything inside the network is safe, Zero Trust treats every user, device, and application as potentially compromised. Access is granted only after rigorous authentication, authorization, and continuous monitoring, regardless of location or network origin.
This approach relies on several core concepts: strict identity verification, least privilege access, micro-segmentation, and real-time analytics. By eliminating implicit trust, Zero Trust minimizes the risk of lateral movement by attackers and reduces the impact of breaches.
Drivers Behind Zero Trust Adoption
Several factors are accelerating the shift to Zero Trust. The rise of remote work and cloud computing has dissolved traditional network boundaries. Employees access resources from various locations and devices, making it harder to enforce security with perimeter defenses alone. Additionally, the proliferation of IoT devices and third-party integrations expands the attack surface, increasing vulnerability.
Regulatory requirements are also pushing organizations toward Zero Trust. Data privacy laws and industry standards demand robust access controls and audit trails. Zero Trust frameworks help meet these obligations by providing granular visibility and control over who accesses what, when, and how.
Key Components of Zero Trust Architecture
Zero Trust is not a single product but a comprehensive strategy. It includes:
- Identity and Access Management (IAM): Continuous authentication and authorization for every user and device.
- Least Privilege: Users and applications receive only the access necessary to perform their tasks.
- Micro-Segmentation: Dividing networks into small, isolated segments to limit the spread of threats.
- Continuous Monitoring: Real-time analytics and threat detection to identify suspicious activity.
- Encryption: Protecting data in transit and at rest to prevent unauthorized access.
Benefits of Zero Trust Security
Adopting Zero Trust delivers multiple benefits. It significantly reduces the risk of data breaches by preventing unauthorized access and limiting the movement of attackers within the network. Organizations gain greater visibility into user activity, enabling faster detection and response to threats.
Zero Trust also supports compliance with regulations such as GDPR, HIPAA, and PCI DSS. Detailed audit logs and access controls make it easier to demonstrate adherence to security standards. The approach is scalable, adapting to cloud environments, hybrid infrastructures, and evolving business needs.
Challenges and Implementation Strategies
Implementing Zero Trust can be complex, requiring cultural change and investment in new technologies. Organizations must map their assets, define access policies, and integrate identity management solutions. Legacy systems may need upgrades or replacements to support Zero Trust principles.
Successful adoption involves a phased approach: starting with critical assets, expanding to broader environments, and continuously refining policies. Employee training and stakeholder engagement are essential to ensure buy-in and effective execution.
The Future of Zero Trust Security
As cyber threats continue to evolve, Zero Trust will become the standard for modern IT systems. Advances in AI and automation will enhance real-time monitoring and adaptive access controls. Integration with cloud-native platforms and edge computing will further extend Zero Trust principles across distributed environments.
Conclusion
Zero Trust Security is mandatory for modern IT systems. By eliminating implicit trust and enforcing rigorous verification, organizations can protect their assets, comply with regulations, and build resilient digital infrastructures. As technology advances, Zero Trust will remain central to effective cybersecurity, ensuring that businesses stay secure in an increasingly connected world.




One Response
hello